HIRT-PUB15003: [tutorial] SSL/TLS implementations 'FREAK' issue
(VU#243585, JVNVU#99125992)
Last Updated: July 27, 2015
1. Overview
Some SSL/TLS implementations accept the use of an export-grade (512-bit or smaller) RSA public key in a non-export RSA key exchange ciphersuite. This flaw could allow an attacker able to act as a Man-in-The-Middle (MiTM) to downgrade algorithm such as an export-grade (512-bit or smaller) RSA key, obtain session keys, and decrypt SSL/TLS traffic. This vulnerability is commonly referred to as "FREAK" (Factoring Attack on RSA-EXPORT Keys).
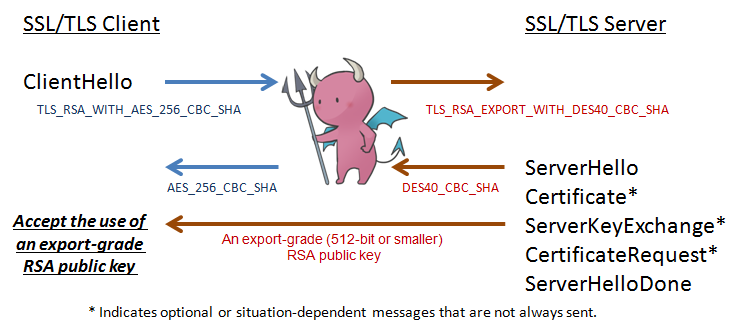 Figure 1. Man-in-The-Middle (MiTM) and algorithm downgrade.
Figure 1. Man-in-The-Middle (MiTM) and algorithm downgrade.
The ServerKeyExchange message is sent by the server only when the ServerCertificate message does not contain enough data to allow the client to exchange a premaster secret such as RSA_EXPORT (if the public key in the server certificate is longer than 512 bits) key exchange methods. Also this ServerKeyExchange message conveys cryptographic information to allow the client to communicate the premaster secret: an export-grade (512-bit or smaller) RSA public key to encrypt the premaster secret with which the client can complete a key exchange. Some SSL/TLS implementations accept the use of this export-grade RSA public key.
2. Affected Systems
+ SSL/TLS libraries and applications
3. Impact
An attacker able to act as a Man-in-The-Middle (MiTM) to downgrade SSL/TLS algorithm such as an export-grade (512-bit or smaller) RSA key, obtain session keys, and decrypt SSL/TLS traffic.
4. Solution
SSL/TLS server and client: Do not offer export grade ciphers
Configure server and client applications not to use export grade ciphersuites such as the followings. These ciphersuites use 512 bit RSA/DH in key exchange phase and 40 bit RC2/RC4/DES in session phase.
TLS_RSA_EXPORT_WITH_RC4_40_MD5 (0x0003)
TLS_RSA_EXPORT_WITH_RC2_CBC_40_MD5 (0x0006)
TLS_RSA_EXPORT_WITH_DES40_CBC_SHA (0x0008)
TLS_DH_DSS_EXPORT_WITH_DES40_CBC_SHA (0x000B)
TLS_DH_RSA_EXPORT_WITH_DES40_CBC_SHA (0x000E)
TLS_DHE_DSS_EXPORT_WITH_DES40_CBC_SHA (0x0011)
TLS_DHE_RSA_EXPORT_WITH_DES40_CBC_SHA (0x0014)
TLS_DH_anon_EXPORT_WITH_RC4_40_MD5 (0x0017)
TLS_DH_anon_EXPORT_WITH_DES40_CBC_SHA (0x0019)
SSL/TLS client: Update SSL/TLS libraries and applications
Some SSL/TLS implementations accept the use of an export-grade (512-bit or smaller) RSA public key in key exchange phase, even when negotiated a non-export RSA key exchange ciphersuite.
OpenSSL (CVE-2015-0204) [January 8, 2015]
RSA silently downgrades to EXPORT_RSA [Client] (CVE-2015-0204)
https://www.openssl.org/news/secadv_20150108.txt
Chrome [March 5, 2015]
Update to Chrome 41
Apple products: Safari, Apple TV etc. (CVE-2015-1067) [March 9, 2015]
About Security Update 2015-002
https://support.apple.com/en-us/HT204413
About the security content of iOS 8.2
https://support.apple.com/en-us/HT204423
About the security content of Apple TV 7.1
https://support.apple.com/en-us/HT204426
Microsoft produtcts: Internet Explorer etc. (CVE-2015-1637) [March 11, 2015]
MS15-031: Vulnerability in Schannel Could Allow Security Feature Bypass (3046049)
https://technet.microsoft.com/library/security/MS15-031
5. Product Information
July 15, 2015
March 9, 2015
6. References
Vulnerability Enumeration
VU#243585: SSL/TLS implementations accept export-grade RSA keys (FREAK attack)
http://www.kb.cert.org/vuls/id/243585
Other Information
RFC2246: The TLS Protocol Version 1.0 - 7.4.3. Server key exchange message
https://tools.ietf.org/html/rfc2246#section-7.4.3
7. Update history
July 27, 2015
- Updated: Product Information in "July 15, 2015".
March 23, 2015
- This webpage was newly created and published.
Masato Terada (HIRT) and Naoko Ohnishi (HIRT)






